The North Korean-linked cybercriminal group known as Kimsuky was connected to the use of a new malicious Google Chrome extension known as TRANSLATEXTdesigned to steal sensitive information as part of an ongoing intelligence gathering operation.
TRANSLATEXT: What is known about this malicious Google Chrome extension
The Kimsuky hacker group it already made itself felt in March 2024 with the TODDLESHARK malware.
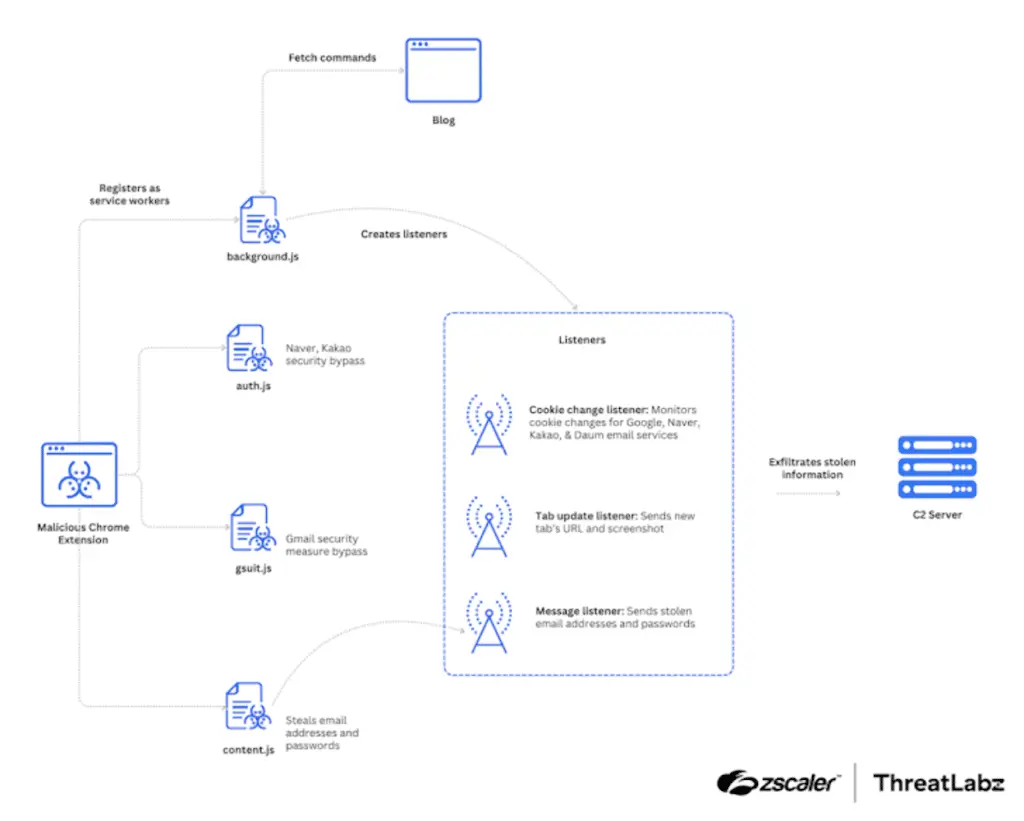
Zscaler ThreatLabz, not surprisingly, has observed the activity at the beginning of March 2024, called the TRANSLATEXT extension, highlighting its ability to collect email addresses, usernames, passwords, cookies and browser screenshots.
Cybersecurity experts believe the campaign was directed against South Korean academiaparticularly against those involved in North Korean political affairs.
Kimsuky is one well-known hacker team of North Korea, and responsible for TRANSLATEXT, active since at least 2012, is responsible among other things for cyber espionage and especially financial attacks aimed at South Korean entities.
Kimsuky may be linked to other North Korean hacker groups: such as the Lazarus group
An affiliated group of the Lazarus cluster and part of the Reconnaissance General Bureau (RGB), it is also track under the names APT43, ARCHIPELAGO, Black Banshee, Emerald Sleet, Springtail and Velvet Chollima.
In the last weeks, The group exploited a known security vulnerability in Microsoft Office (CVE-2017-11882) to distribute a keylogger and used job-themed lures in attacks targeting the aerospace and defense industries with the goal of releasing an espionage tool with data collection and secondary payload execution capabilities.
“The backdoor, which does not appear to have been publicly documented before, allows the attacker to perform basic reconnaissance and release additional payloads to take control or remotely control the machine“, has said the cybersecurity company known as CyberArmor; The company has given this hacking campaign the code name “Niki”.
TRANSLATEXT: How this malicious extension works is not fully known
The exact manner of initial access associated with the newly discovered activity is currently unclear, although the group is known to exploit attacks spear-phishing and social engineering to activate the chain of infection.
The starting point of the attack is a ZIP archive which presents itself as a document on Korean military history and which contains two files: a Hangul Word Processor document and an executable.
Launching the executable involves retrieving a PowerShell script from an attacker-controlled server, which, in turn, exports information about the compromised victim to a GitHub repository and download additional PowerShell code via a Windows shortcut file (LNK).
Zscaler claimed to have found the account GitHubcreated on February 13, 2024, which briefly hosted the TRANSLATEXT extension under the name “GoogleTranslate.crx”, although its distribution method is currently unknown.
How this malicious Google Chrome extension disguises itself
“These files were present in the repository on March 7, 2024, and were deleted the next day, implying that Kimsuky intended to minimize exposure and use the malware for a short period to target specific individuals“said security researcher Seongsu Park.

TRANSLATEXT, which masquerades as Google Translateembeds JavaScript code to bypass the security measures of services like Google, Kakao, and Naver; siphon email addresses, credentials, and cookies; capture browser screenshots; and exfiltrate stolen data.
It is also designed to retrieve commands from a Blogger Blogspot URL in order to take screenshots of new tabs opened and clear all cookies from the browser, among other things.
“One of the Kimsuky group’s primary objectives is to conduct surveillance on academic and government personnel to gather valuable intelligence,” Park said.
#TRANSLATEXT #Malicious #Google #Chrome #Extension














