A serious security flaw has been revealed in the WPML plugin for WordPress, used for managing multilingual sites, which could allow authenticated users to remotely execute malicious code under certain circumstances.
It should be noted that less than a month ago there was another problem on another WordPress plugin, see the LiteSpeed case.
WPML Plugin Vulnerability
The vulnerability, identified as CVE-2024-6386 (CVSS score: 9.9), affects all versions of the plugin prior to 4.6.13, released on August 20, 2024.
On June 19, 2024, a report was received for a Remote Code Execution vulnerability via Twig Server-Side Template Injection in WPML, a WordPress plugin with over 1,000,000 active installations and This vulnerability can be exploited to execute remote code by authenticated users with access to the post editor.
This issue, due to the lack of input validation and sanitization, allows an authenticated attacker, with Contributor level access or higher, to execute code on the server.
What is the purpose of the WPLM plugin?
WPML is a popular plugin used to create multilingual WordPress sites, with over a million active installations, as just mentioned.
Security researcher stealthcopter, who discovered and reported the CVE-2024-6386 vulnerability, said that the issue lies in the handling of shortcode of the plugin, used to insert content into posts, such as audio, images and videos.
“Specifically, the plugin uses Twig templates to render content in shortcodes, but fails to properly sanitize the input, leading to server-side template injection (SSTI)“, has explained the researcher.
The SSTI, as the name suggests, is verify when an attacker is able to use the native template syntax to inject a malicious payload into a web template, which is then executed on the server. An attacker could then exploit this vulnerability to execute arbitrary commands, allowing them to take control of the site.
“This WPML update resolves a security vulnerability that could allow users with certain permissions to perform unauthorized actions“, they have affirmed the maintainers of the plugin, OnTheGoSystems. “This issue is unlikely to occur in real-world scenarios. It requires users to have editing permissions on WordPress and the site to use a very specific configuration..”
Luckily The plugin was patched on August 20, 2024, so plugin users are advised to apply the latest patches to mitigate potential threats.
Technical Analysis of the WPML Flaw
The plugin provides a shortcode ([wpml_language_switcher]) which can be used to add a custom language switcher with a Twig template; the code calls the function callback() in the class WPML_LS_Shortcodeswhich in turn calls the render() function in the class WPML_LS_Public_API.
Below is the code for this plugin:
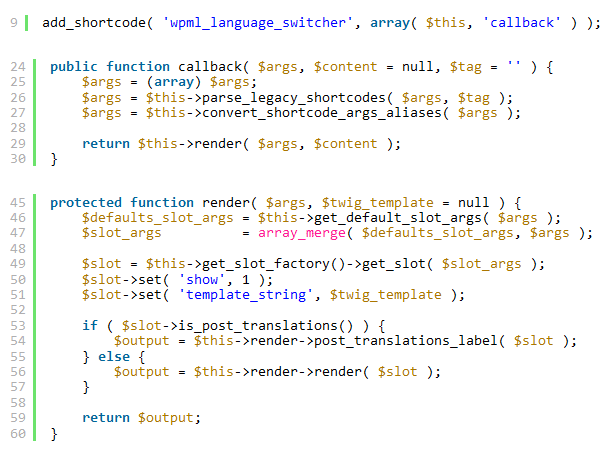
This function renders the provided Twig template into the shortcode content but fails to sanitize it, making it possible to inject malicious code into a server-side template.
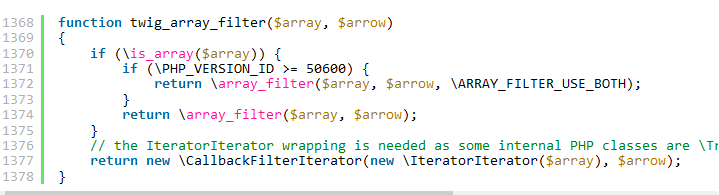
Twig has built-in functions and filters that ultimately perform specific PHP functions. For example, the filter filter uses the PHP function array_filter(), which can be used for questionable function calls:
Like all remote code execution vulnerabilities, This can lead to complete site compromise through the use of webshells and other techniques.
Now, I’ve been very brief in explaining this problem (knowing that not everyone is an expert in JavaScript, Python, C++ and programming languages in general; but to make it short, you just need to know that a few incorrect lines of code can really ruin everything and allow cybercriminals to exploit such code errors.
#WPML #WordPress #Plugin #Critical #Vulnerability







