A campaign of malvertising (malicious advertisement, often with deceptive links) is exploiting hacked installers of popular software like Google Chrome and Microsoft Teams to spread a backdoor called Oyster (also known as Broomstick and CleanUpLoader).
The research behind Oyster
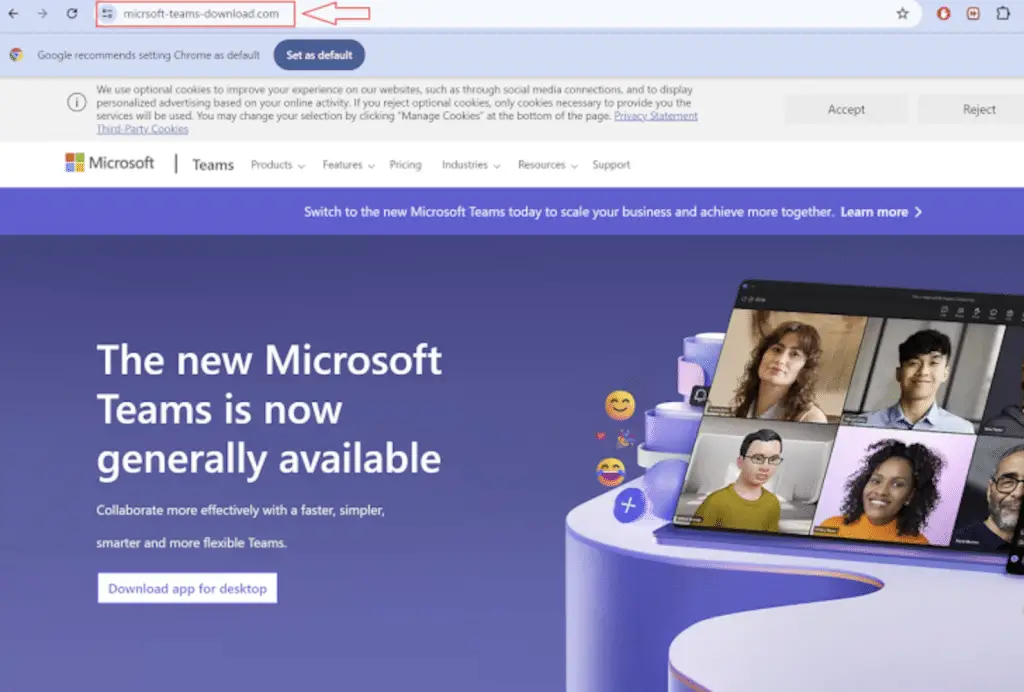
According to reported from Rapid7, Websites similar to legitimate ones have been identified as hosting malicious payloads to which users are redirected after searching for them on search engines such as Google and Bing.
Cybercriminals lure unsuspecting users to fake websites that claim to contain legitimate software; however, attempting to download the installation file, instead of starting the setup, instead starts a malware infection chain.
Specifically, the executable serves as a gateway to the backdoor called Oyster, capable of gathering information about the compromised host, communicating with an encrypted command and control (C2) address, and supporting remote code execution.
While Oyster has previously been deployed via a dedicated loader component known as Broomstick Loader (aka Oyster Installer), the latest attack chains involve direct deployment of the backdoor. The malware is believed to be associated with ITG23a Russian-linked cybercriminal group known for TrickBot malware.
What is the modus operando of the Oyster malware
The execution of the malware is followed by the installation of the legitimate Microsoft Teams software in an attempt to maintain the deception and avoid raising suspicion; Rapid7 indeed observed that the malware was used also to launch a PowerShell script responsible for establishing persistence on the system.
This announcement comes at the same time as the discovery of a cybercriminal group known as Rogue Raticate (also known as RATicate), who are behind an email phishing campaign that uses PDF excuses to trick users into clicking on malicious URLs and deploy NetSupport RAT.
Symantec cybersecurity researchers’ analysis
Symantec has declared: “If a user is successfully tricked into clicking on the URL, they will be guided through a traffic distribution system (TDS) along the infection chain and, eventually, have the NetSupport remote access tool installed on their device.”
Additionally, it coincides with the emergence of a new phishing-as-a-service (PhaaS) platform called ONNX Store that allows customers to orchestrate phishing campaigns using QR codes embedded in PDF attachments that direct victims to data harvesting pages. credentials.

ONNX Store, which also offers bulletproof hosting and RDP services via a Telegram bot, is believed to be a rebranded version of the phishing kit known as Caffeinepreviously documented by Google-owned Mandiant in October 2022, run by an Arabic-speaking cybercriminal called MRxC0DER.
In addition to using Cloudflare’s anti-bot mechanisms to avoid detection by phishing website scanners, URLs distributed via quishing campaigns contain Encrypted JavaScript which is decoded during page load to collect victims’ network metadata and 2FA token relay (two-factor verification).
“ONNX Store has a two-factor authentication (2FA) bypass mechanism that intercepts two-factor authentication requests from victims“, has said EclecticIQ researcher Arda Büyükkaya. “Phishing pages resemble real Microsoft 365 login interfaces, tricking targets into entering their authentication credentials.”
Conclusion
You should always check which sites you are visiting, and never click randomly: it is essential to check that the URL is legitimate before downloading anything, as it may not be detected immediately by the antivirus (if the definitions are still missing), just as it may happen with malware like Oyster.
#Oyster #Backdoor #malware #malicious #pseudo #advertising














