An alleged cyber espionage group linked to China, a was considered as responsible for a sustained attack against an unnamed organization located in East Asia over a period of approximately three years, with the attacker establishing persistence using older F5 BIG-IP devices and using them as a command and control (C&C) internal for defense evasion purposes.
What is this cyber espionage campaign about?
Cybersecurity firm Sygnia, which responded to the intrusion in late 2023, is monitoring the activity under the name Velvet Ant, characterizing it as possessing robust capabilities to rapidly adapt and pivot their tactics to counter remediation efforts.
“Velvet Ant is a very sophisticated and innovative cybercriminal group“, has said the Israeli company in a technical report shared with various foreign newspapers. “They collected sensitive information over a long period of time, focusing on customer and financial information.”
The attack chains involve the use of a known backdoor called PlugX (bita abcge Korplug), a modular remote access trojan (a Trojan horse, a true conduit for cyber espionage) (essentially a RAT, as occurred on other occasions) widely used by cyber espionage operators with links to Chinese interests; PlugX is known to rely heavily on a technique called DLL side-loading to infiltrate devices.
Attempting to disable devices
Sygnia said it also identified attempts by cyber espionage campaign authors to disable endpoint security software before installing PlugX, with open-source tools like Impacket used for lateral movement.
Also identified, as part of incident response and remediation efforts, was a reworked variant of PlugX that used an internal file server for C&C, thus allowing malicious traffic to mix with legitimate network activity.
“This meant that the cybercriminal group deployed two versions of PlugX within the network“, the company noted. “The first version, configured with an external C&C server, was installed on endpoints with direct access to the internet, facilitating the exfiltration of sensitive information. The second version did not have a C&C setup and was deployed exclusively on legacy servers.“
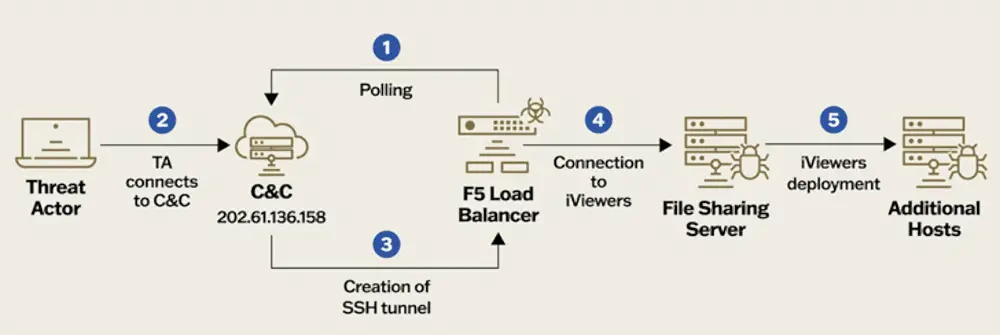
Notably, the second variant was found to abuse outdated F5 BIG-IP devices as a covert channel to communicate with the external C&C server by issuing commands via a reverse SSH tunnel, highlighting Once again how compromising edge devices can allow cybercriminals to gain persistence over long periods of time.
“Only one thing is needed for a mass exploitation incident to occur, and that is a vulnerable edge service, i.e. a piece of software accessible from the internet“, has said WithSecure in a recent analysis, adding: “Devices like these are often intended to make a network more secure, yet time and again vulnerabilities have been discovered in such devices and exploited by attackers, providing a perfect foothold in a target network.”
The final analysis of the F5 devices
Subsequent forensic analysis of the compromised F5 devices also revealed the presence of a tool called PMCD that queries the cyber espionage group’s C&C server every 60 minutes for commands to execute, as well as additional programs to capture network packets and a SOCKS tunneling utility called EarthWorm used by other hacker groups such as Gelsemium and Lucky Mouse.

The exact initial access vector (whether spear-phishing or exploitation of known security flaws in internet-exposed systems) used to breach the environment targeted by cyber espionage is currently unknown.
The development of this cyber espionage story follows the emergence of new clusters linked to China traced as Unfading Sea Haze, Operation Diplomatic Specter And Operation Crimson Palace which have been observed targeting Asia with the aim of collecting sensitive information.
#Cyber #espionage #Asia #devices








