A new Android banking trojan called Nexus has already been adopted by several threat actors to attack 450 financial applications and conduct fraud, a similar case occurred a while back.
Nexus: What Do We Know About This Banking Trojan?
“Nexus appears to be in the early stages of development“, has declared Italian cybersecurity firm Cleafy in a report released this week.
“Nexus provides all the main functions to perform ATO (Account Takeover) attacks against banking portals and cryptocurrency services, such as credential stealing and SMS interception“.
The trojan, which appeared on various hacking forums earlier this year, is being advertised as a subscription service for its customers for a monthly fee of $3,000. The details of the malware were documented for the first time by Cyble earlier this month.
However, there are indications that the malware may have been used in real-world attacks as early as June 2022, at least six months before its official announcement on darknet portals.
According to security researcher Rohit Bansal (@0xrb) and confirmed by the malware authors in their Telegram channel, most of the infections of this new trojan have been reported in Turkey.
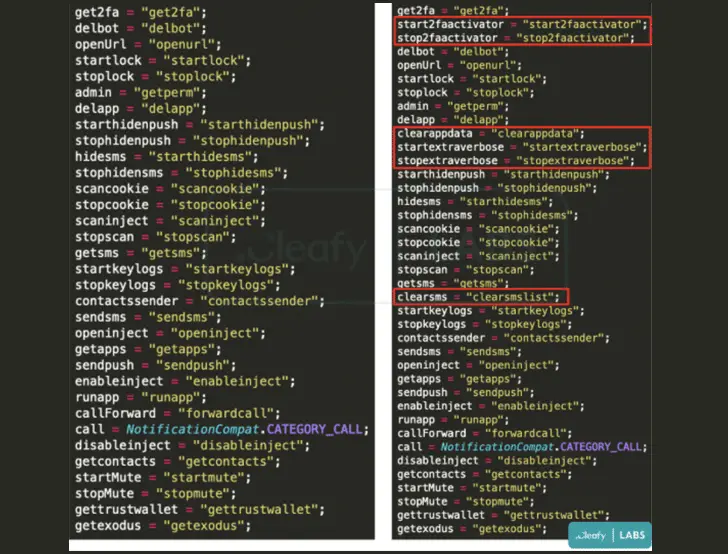
Nexus is also said to go hand in hand with even another banking trojan called SOVAreusing parts of its source code and incorporating a ransomware module that appears to be under active development.
A noteworthy point is that the Nexus Trojan is the same malware that Cleafy initially classified as a new variant of SOVA (called v5) in August 2022.
Interestingly, Nexus authors have established explicit rules prohibiting the use of their malware in Azerbaijan, Armenia, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Russia, Tajikistan, Uzbekistan, Ukraine, and Indonesia.
The malware, like other banking trojans for that matter, contains functionality to take over cryptocurrency and banking related accounts using overlay attacks and keylogging to steal users’ credentials.
Furthermore, it is capable of reading two-factor authentication (2FA) codes from SMS messages and the Google Authenticator app through the abuse of Android’s accessibility services.
Some new additions to the feature list are the ability to remove received SMS messages, activate or stop the 2FA theft module, and periodically update itself by pinging a command-and-control (C2) server.
“The Malware-as-a-Service model allows criminals to monetize their malware more efficiently by providing a ready-made infrastructure to their customers, who can then use the malware to attack their targets“, said the researchers.
Development comes while it was discovery an update to an information-stealing malware for Windows called BlackGuard with functionality clipperthe ability to propagate across removable media and shared devices, and even download and execute additional payloads.
How to defend against attacks like Nexus or in general?
If you suspect or confirm a cyber-attack or malware like the one described here, it’s important to take immediate action to protect your data and devices.
Here are some tips:
- Update your device software and applications, including the latest security patches.
- Only use legitimate software and applications from trusted sources.
- Avoid clicking on suspicious links or attachments in messages or emails.
- Use robust anti-virus and anti-spyware protection.
- Use strong passwords and change old ones regularly.
- Do not share sensitive personal or financial information via email or text.
- Be careful with banking or financial information that you provide online or through applications, especially if it requires you to log into your account.
- Regularly monitor financial accounts for suspicious activity.
If you suspect your device has been compromised, it’s important to disconnect your device (or devices) from the network immediately and contact a cybersecurity expert to help remove the malware and restore device security and perhaps a wipe of antimalware.
#Nexus #banking #trojan #infects #applications












