Microsoft said on Tuesday that it has taken steps to disable fake Microsoft Partner Network (MPN) accounts used to build applications OAuth malicious as part of a phishing campaign designed to violate organizations cloud environments and steal email.
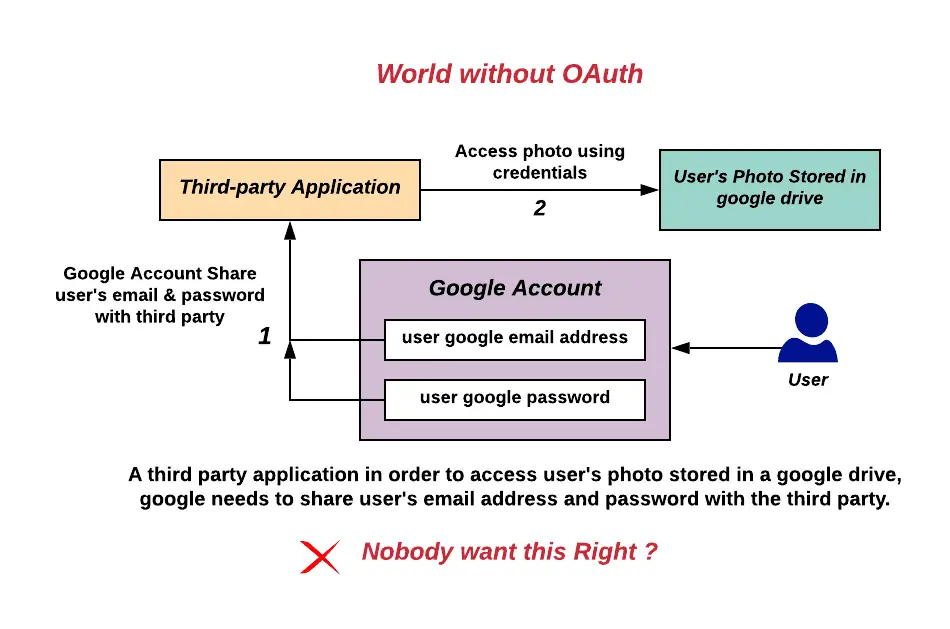
What is the OAuth protocol in a nutshell
For the uninitiated OAuth is a protocol that was designed for HTTP sites, citing wikipedia “allows an authorization server to issue an access token to a third-party client, subject to approval by the user who owns the resource to be accessed.”
Basically you send a signal with this protocol and on the other side someone (or some program) authorizes you to “enter”.
How the abuse of this protocol happened
“The applications created by these malefactors were then used in a consent phishing campaign, which tricked users into granting permissions to the fraudulent apps“, has said US tech giant. “This phishing campaign targeted a subset of customers primarily based in the UK and Ireland“.
Consent phishing is an attack social engineering whereby users are tricked into granting permissions to malicious cloud applications, which can then be used as “weapons” to gain access to legitimate cloud services and sensitive user data.
The Windows maker said it became aware of the campaign on December 15, 2022 and has since alerted affected customers by email; the company also noted that the perpetrators of these cyberthreats abused consent to filter mailboxes.
Additionally, Microsoft said that it has implemented additional security measures to enhance the auditing process associated with the Microsoft Cloud Partner Program (formerly known as MPN) and minimize the potential for fraudulent behavior (exploiting OAuth protocol bugs) in the future.
Disclosure coincides with a report published by Proofpoint on how bad actors exploited the OAuth protocol bug successfully the status of “verified publisher” by Microsoft to infiltrate organizations’ cloud environments.
What is remarkable about this campaign is that by imitating famous brands, the hackers have also managed to trick Microsoft into getting the verified blue badge. “The actor used fraudulent partner accounts to add a verified publisher to OAuth app registrations created in Azure AD“explained the company.
These attacks, which first appeared on December 6, 2022, used similar versions of legitimate applications like Zoom to trick targets into authorizing access and facilitate data theft. Targets included finance, marketing, managers and senior executives.

Proofpoint noted that malicious OAuth protocol applications had “far-reaching delegated permissions” such as reading emails, adjusting mailbox settings, and accessing files and other data linked to the user’s account .
He also stated that, unlike a previous campaign that compromised existing Microsoft verified publishers to exploit OAuth app privileges, the latest attacks are designed to impersonate legitimate publishers to be verified and distribute the unauthorized applications.
Two of the applications in question were named “Single Sign-on (SSO),” while the third application was named “Meeting” in an attempt to masquerade as video conferencing software; all three applications, created by three different publishers, targeted the same companies and leveraged the same infrastructure controlled by the “attackers”.
“Potential impact to organizations includes compromised user accounts, data exfiltration, brand abuse of impersonated organizations, corporate email compromise (BEC) fraud, and mailbox abuse“said the corporate security firm.

It appears that the campaign ended on December 27, 2022, one week after Proofpoint notified Microsoft of the December 20 attack, and the applications were subsequently disabled.
The results demonstrate the sophistication with which the attack was mounted, not to mention the circumvention of Microsoft’s security protections and the misuse of the trust users place in vendors and enterprise service providers.
This isn’t the first time bogus OAuth applications have been used to target Microsoft’s cloud services; in January 2022, Proofpoint disclosed in detail another threat activity named OiVaVoii which has targeted high-level executives to take control of their accounts.
Then, in September 2022, Microsoft has revealed that it dismantled an attack that used malicious OAuth applications deployed on compromised clouds to eventually take over Exchange servers and distribute spam.
#OAuth #Microsoft #verified #publishers #attack