The United States Cybersecurity and Infrastructure Security Agency (CISA) has added Wednesday one critical vulnerability that affects Fortinet products to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.
FortiOS and other software: all vulnerabilities disclosed by CISA from Fortinet to Palo Alto Networks
Vulnerability, tracked as CVE-2024-23113 (CVSS score: 9.8), concerns remote code execution cases affecting FortiOS, FortiPAM, FortiProxy and FortiWeb.
“An externally controlled format vulnerability [CWE-134] in the FortiOS fgfmd daemon can allow an unauthenticated remote attacker to execute malicious code or commands via specially crafted requests“, ha observed Fortinet in an advisory regarding the flaw in February 2024.
As often happens in these casesthe bulletin provides few details on how this vulnerability is being actively exploited or who is using it and more importantly against whom.
In light of active exploitation, Federal Civilian Executive Branch (FCEB) agencies are required to apply vendor-provided mitigations by October 30, 2024 to ensure maximum protection.
Palo Alto Networks Reveals Critical Bugs in Its “Expedition” Program
The new development comes as Palo Alto Networks disclosed several security flaws in Expedition that could allow an attacker to read database contents and arbitrary files, as well as write arbitrary files to temporary storage locations on the system.
“Combined, this includes information such as usernames, plaintext passwords, device configurations, and PAN-OS firewall API keys,” he declared Palo Alto Networks in an advisory Wednesday.
The vulnerabilities, which affect all versions of Expedition prior to 1.2.96, are listed below:
- CVE-2024-9463 (CVSS Score: 9.9) – An operating system (OS) command injection vulnerability that allows an unauthenticated attacker to execute arbitrary OS commands as root
- CVE-2024-9464 (CVSS Score: 9.3) – An OS command injection vulnerability that allows an authenticated attacker to execute arbitrary OS commands as root
- CVE-2024-9465 (CVSS score: 9.2) – An SQL injection vulnerability that allows an unauthenticated attacker to reveal the contents of the Expedition database
- CVE-2024-9466 (CVSS score: 8.2) – A sensitive information plaintext storage vulnerability that allows an authenticated attacker to reveal usernames, passwords, and firewall API keys generated using those credentials
- CVE-2024-9467 (CVSS score: 7.0) – A reflected cross-site scripting (XSS) vulnerability that allows the execution of JavaScript malicious in the context of an authenticated Expedition user’s browser if that user clicks on a malicious link, enabling phishing attacks that could lead to theft of the Expedition browser session
The company credited Horizon3.ai’s Zach Hanley with the discovery and reporting of CVE-2024-9464, CVE-2024-9465 And CVE-2024-9466and to Enrique Castillo of Palo Alto Networks CVE-2024-9463, CVE-2024-9464, CVE-2024-9465 And CVE-2024-9467.
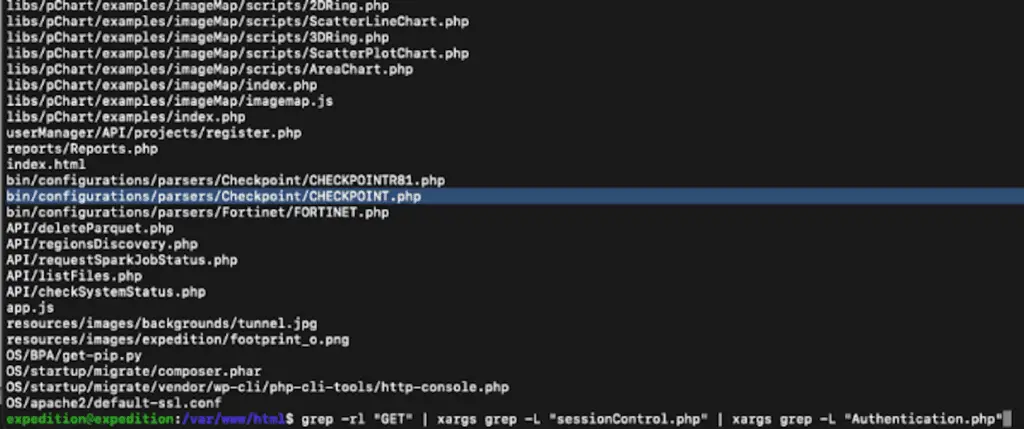
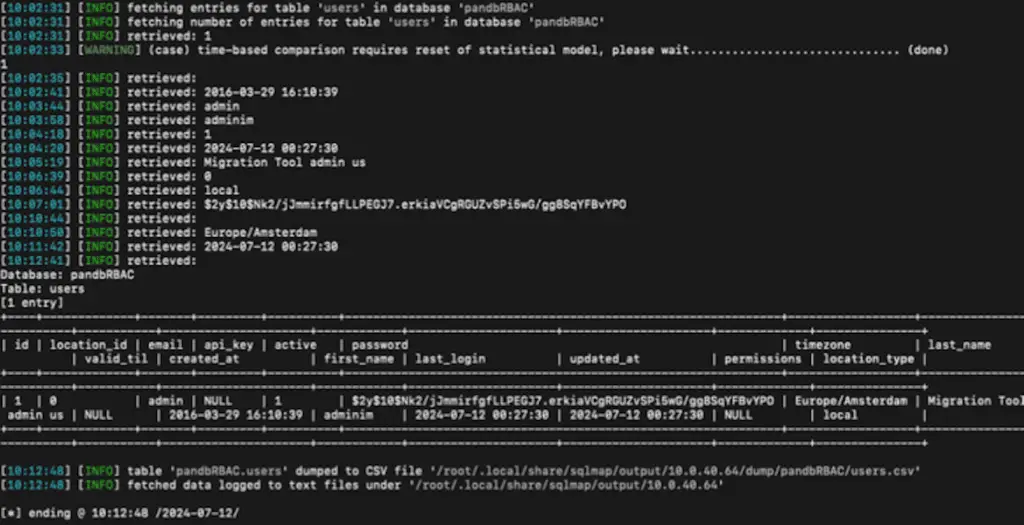
There is no evidence that these vulnerabilities have ever been exploited in real contexts, although it has been reported that steps for reproduce the problem are already in the public domain, thanks to Horizon3.ai.
There are approximately 23 Expedition servers exposed to the internet, most of which are located in the United States, Belgium, Germany, the Netherlands and Australia. As mitigations, it is recommended to limit access to authorized users, hosts or networks and to turn off the software when not in active use.
Cisco Fixes a flaw in the Nexus Dashboard Fabric Controller
Last week, Cisco released patches to fix a critical command execution flaw in the Nexus Dashboard Fabric Controller (NDFC), caused by improper user authorization and insufficient validation of command arguments.
Tracked as CVE-2024-20432 (CVSS score: 9.9), could allow an authenticated, remote attacker, with limited privileges, to perform a command injection attack against an affected device; it is worth saying that (fortunately!) the vulnerability was fixed in NDFC version 12.2.2 and that versions 11.5 and earlier are not susceptible to this security flaw.
“An attacker could exploit this vulnerability by sending constructed commands to an affected REST API endpoint or via the web UI,” he declared the company. “A successful exploit could allow the attacker to execute arbitrary commands on the CLI of a Cisco NDFC managed device with network administrator privileges.”
#CISA #Warning #Palo #Alto #Fortinet #security #patches








